New Malware 'GoldPickaxe' Is Stealing People's Faces To Create Deepfakes For Bank Fraud
The attacks specifically target the Asia-Pacific region but they can spread to other regions as well.
Feb. 16 2024, Published 2:37 a.m. ET
A new malware is circulating on Android and iOS devices that is capable of stealing victims' faces and biometric data to generate deepfakes and gain unauthorized bank access or to steal identity or files. The trojan called "GoldPickaxe" was discovered by a software company called Group IB. While the company's Threat Intelligence team noted that the attacks specifically target the Asia-Pacific region, with victims in Thailand and Vietnam, the malware is projected to spread across the globe.
What Is the GoldPickaxe Malware?
The distribution of the "Gold Pickaxe" trojan is thought to have commenced around October 2023 and remains ongoing. This activity is linked to the broader GoldFactory campaign, that was initiated in June 2023, with the deployment of another trojan known as "Gold Digger."
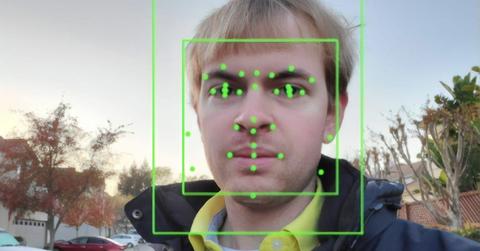
Once installed onto an Android device, the trojan takes the form of a fake government app. It then operates semi-autonomously, manipulating functions in the background, capturing the victim's face, intercepting SMS, asking for ID documents, and proxying network traffic through the infected device.
On iOS devices, however, the malware establishes a web socket and carries out various commands. These include sending device information, requesting the victim to take an image of their ID card, requesting a video of their face, displaying a bogus "device in use" message, accessing a photo library, and more.
However, as per the Android version, the trojan performs more malicious activities using over 20 different bogus apps as cover. Apple, on the other hand, has higher security restrictions, limiting the trojan’s operation.
How Does GoldPickaxe Steal Your Face?
In the scam, victims are approached through phishing or smishing messages written in their native language on the LINE app. These messages impersonate government authorities or services. The scammers then attempt to trick the victims into installing fraudulent apps disguised as "Digital Pension" apps, hosted on websites impersonating Google Play. The malware gains access to the victim’s device and can carry out criminal operations.
For instance, a victim in Hanoi, Vietnam, received a call from a person claiming to be a government official, according to a local news report. The imposter then asked the man to integrate an identification code at home and download fake Public Service software. The man went on to execute the app’s instructions, including scanning the camera to identify the face. The next day, he discovered that the stock account he had installed on his phone had lost control, and about 3 billion VND (approximately $122,424) in the account was transferred elsewhere.

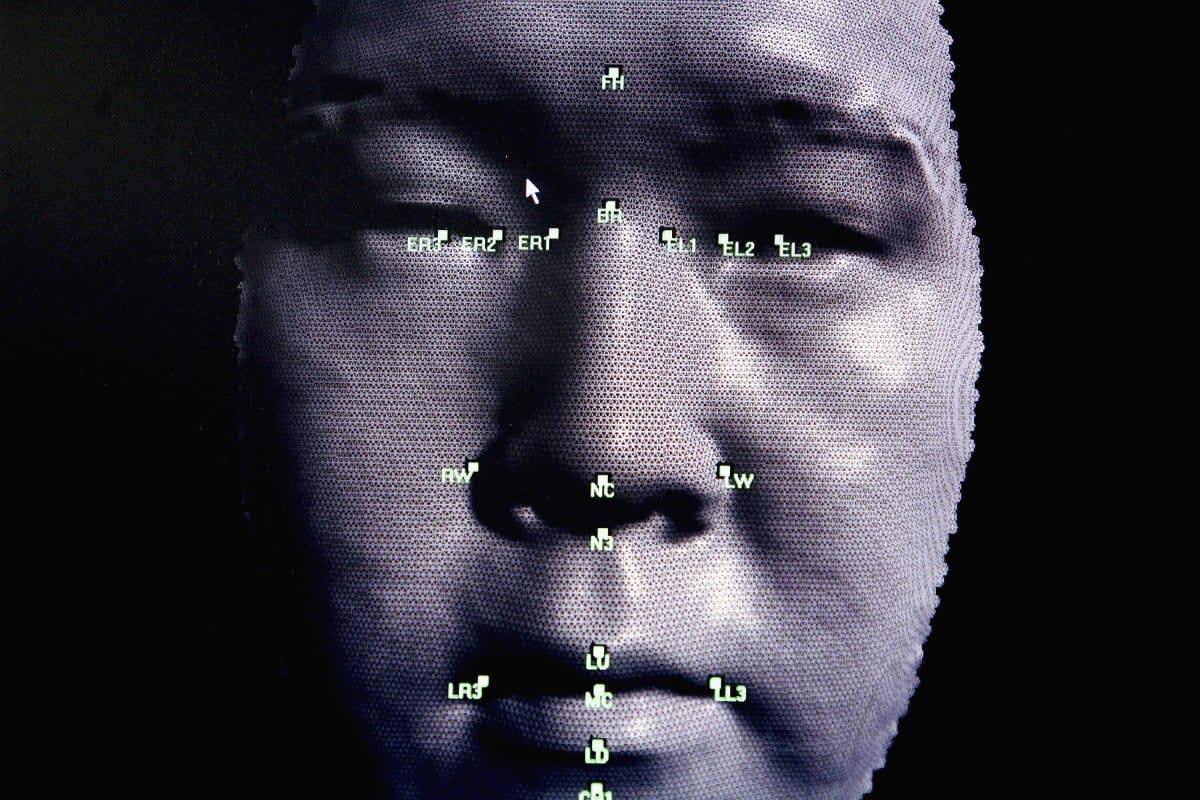
According to Group IB, the application uses the stolen biometric data for AI face-swapping services to create deepfakes of the victims. This allows the scammers to autonomously access the victim’s banking application as facial recognition is actively used by Thai financial organizations for verification.
Who is behind GoldPickaxe?
Group-IB attributes the fraud to the highly sophisticated Chinese-speaking threat group, "GoldFactory" as debugging strings found in the malware variants included prompts in the Chinese language. GoldFactory, also responsible for developing other malware strains such as "GoldDigger," "GoldDiggerPlus," and "GoldKefu," uses various tactics, including impersonation, creating and using fake banking websites, using fake bank alerts, using fake call screens, and more. Reportedly, the group has separate development and operator groups dedicated to specific regions.
Group-IB researchers also found similarities between Goldfactory’s malware and "Gigabud," a disruptive banking trojan operating in Thailand, Vietnam, and some countries in Latin America. However, there is not enough evidence to attribute the development of Gigabud to GoldFactory yet. However, suspicions of it being involved in distribution remain.
