Wormhole Exploit: How Did Hackers Make Off With $320M Ether?
Blockchain bridge Wormhole fell victim to a $320 million hack—the second-largest hack in DeFi history. How did the Wormhole hack happen?
Feb. 3 2022, Published 11:05 a.m. ET
Blockchain bridge Wormhole is at the center of a major exploit that temporarily left hackers with the equivalent of $320 million Ether. The Wormhole hack is the second-largest hack in DeFi history.
How did the Wormhole hack happen and what does it mean for investors using any of the blockchains it bridges—like Ethereum, Solana, and Polygon?
Wormhole hackers made off with 120,000 Ether.

On Feb. 2, crypto company Wormhole wrote on Twitter, “The wormhole network is down for maintenance as we look into a potential exploit. We will provide updates here as soon as we have them.”
Shortly after, reports came to light that hackers made off with 120,000 Ether, or about $320 million.
The stolen cryptocurrency came in the form of wETH, which is Wormhole’s token that trades on the Ethereum blockchain. Wormhole’s token is designed to operate on a 1:1 value equivalency with Ether, but wETH inflated when hackers cashed out 120,000 tokens. As a result, Wormhole was required to add Ether to balance the values between the assets.
What does Wormhole do?
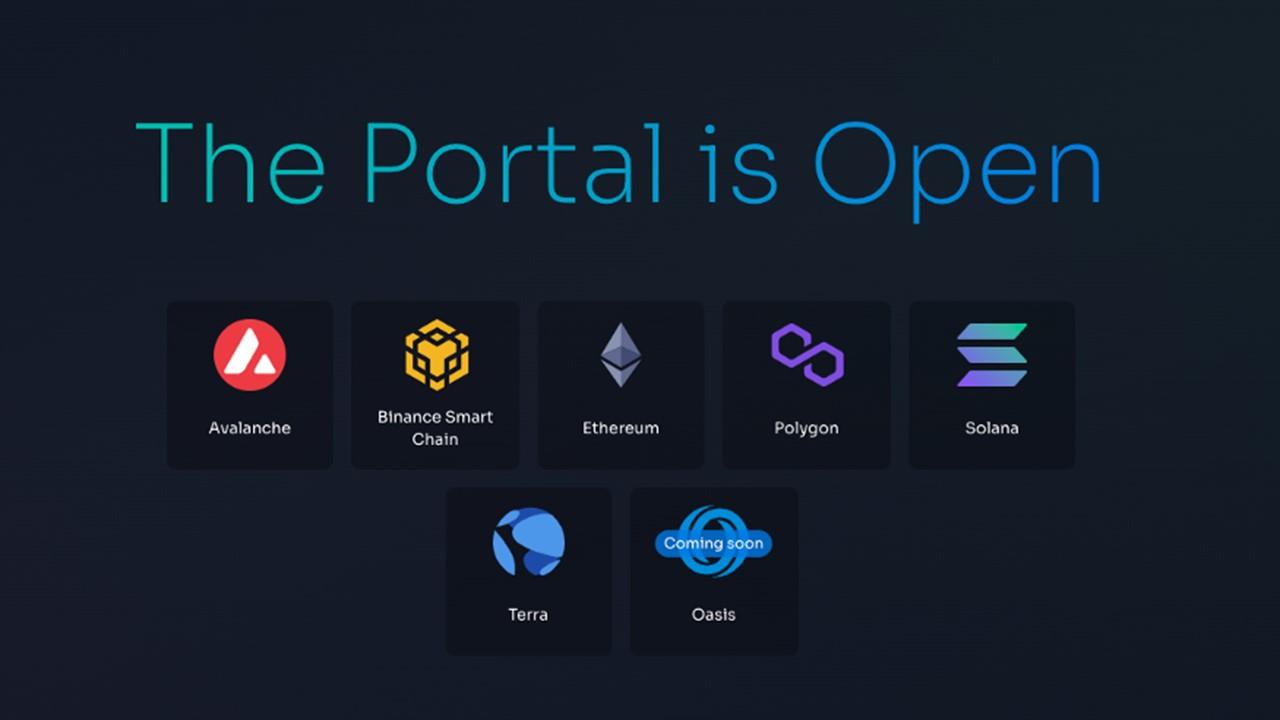
Wormhole is a blockchain bridge, which means that it’s a protocol that supports the integration of different blockchains—Terra, Solana, Ethereum, Binance Smart Chain, Avalanche, and Polygon. People can use Wormhole to integrate apps to live across chains simultaneously. Also, Wormhole-wrapped NFTs are a thing.
When you think about how interconnected Wormhole is with the rest of the crypto ecosystem, a hack this size feels that much more threatening.
Wormhole isn't the only DeFi hack.
The week before the Wormhole hack, another exploit cost a DeFi platform big. Hackers nabbed $80 million in assets from Qubit Finance.
The Wormhole hack is the result of a three-part transaction that took place on the Wormhole bridge. About an hour after the last transaction, Wormhole offered the hackers $10 million to return the tokens in a white-hat agreement. Sometimes, hackers will exploit DeFi technology to make the platforms aware of their vulnerabilities and accept a reward in return for the stolen tokens.
Whatever the case, Wormhole found 120,000 Ether somewhere. Users' funds have been restored, which was Wormhole’s biggest concern at the time. Now, the bridge is focused on continuing negotiations and patching vulnerabilities.
What’s next for Wormhole and the greater DeFi?
DeFi hacks are a dime a dozen, which is just one reason why the U.S. government is eager to regulate crypto. However, decentralized finance operates on the premise of being decentralized, so players like Wormhole protocol are sure to find other ways to patch those vulnerabilities.