Healthcare Assets are a Lucrative Target
A highly lucrative target But chronic underspending by providers and ease of access to their networks only partially accounts for the rise of healthcare system cyber attacks. The healthcare sector is also a highly lucrative target for would-be intruders. Patient EHRs, for example, contain data that can be sold, used for medical identity theft or […]
March 9 2017, Published 2:31 p.m. ET
A highly lucrative target
But chronic underspending by providers and ease of access to their networks only partially accounts for the rise of healthcare system cyber attacks. The healthcare sector is also a highly lucrative target for would-be intruders. Patient EHRs, for example, contain data that can be sold, used for medical identity theft or submitted in fraudulent claims for valuable prescription drugs and equipment. And unlike credit cards they cannot be canceled and reissued. According to Symantec and HIMSS, stolen patient data can fetch up to 50 times more than a social security or credit card number on dark web peer-to-peer markets. And increasingly, hospital IT networks are becoming the target of so-called ransomware attacks, in which malware is used to encrypt critical databases and shared files on facility computers or servers, blocking user access. Attackers then demand payment in exchange for unlocking the data. Given that their need to access important information such as patient drug histories is often highly time-sensitive, healthcare providers are more likely to be the deliberate objects of this tactic. In March, for example, the Hollywood Presbyterian Medical Center paid a ransom of 40 bitcoins ($17,000) to regain access to its electronic health record system.
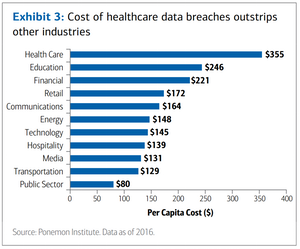
Indeed, the total organizational cost of a cybersecurity breach is typically much higher in the healthcare sector than in other industries. Along with reputational risk and denial of service, which in some instances can put patient health in jeopardy, providers can face litigation costs from HIPAA violations, not to mention industry-wide costs from the inhibition of data sharing between caregivers for fear that their counterparts may not be secure. Across a range of industries examined by the Ponemon Institute in its 2016 Cost of Data Breach study, healthcare ranked the highest on its per capita data breach cost (defined as cost per compromised personal record). At $355, the sector was well above second-place education at $246 and third-place financial services at $221, and more than double the $158 industry average (see Exhibit 3).
The level of spending needs to rise
From the point of view of vulnerability, potential payoff for intruders and potential cost to the industry, it is clear that the level of spending on cyber defense by the healthcare sector will need to rise. In the U.S., healthcare spending already accounts for over 17% of GDP, and as the data vulnerability challenge persists, we should expect the sector to become a major driver of IT security spending. Indeed there are early indications that industry participants may already be starting to place more emphasis here in response to the growing number of attacks. Not only has the FDA warned about security for a specific device, but earlier this year it issued broader guidance on stronger network and endpoint security for the industry as a whole. And a February 2016 International Data Corporation Health Insights study examining the results of an earlier survey revealed that 40% of providers now report their IT budgets to be growing, with security strategies such as network monitoring among the top drivers.
Over the coming years, we expect the healthcare sector to emerge as a key driver of cybersecurity spending within our Innovation investment theme. We believe this will add to the growth in global IT security spending, to the advantage of advanced threat protection software vendors. Healthcare facilities that move first on upgrading network security are likely to see more patient volume as public awareness of the risk posed by vulnerable systems increases. And we would also expect medical hardware manufacturers that develop stronger security features (such as voice activation or biometric scanning) to benefit. With the growing push by the FDA to improve industry standards, and the high cost of potential breaches from compromised devices, providers are likely to make security an increasing priority in their equipment purchase decisions.
